This is an interesting type of story that we hear about in mainstream media every now and then – and that is the finding of critical security weaknesses in widespread technology, particularly those that deal with financial transactions of one kind or another. This time around, it’s flaws in the Chip-and-PIN technology that is widely used in credit and debit cards throughout Europe and particularly the UK.
This particular security flaw has been discovered by computer scientists at Cambridge University, who are saying that it will require the entire system to be replaced in order to circumvent the issue. Professor Ross Anderson has even stated that: “we think this is one of the biggest flaws that we’ve uncovered – that has ever been uncovered – against payment systems, and I’ve been in this business for 25 years“.
Basically, the technique allows the use of a stolen card without any need for the correct PIN number – which is achieved by using a fake card in the shop’s actual terminal and the stolen card interfaced with special software somewhere else on your person, such as a backpack. The technique is even capable of working with point-of-sale systems online, although it apparently doesn’t work at ATMs. The team from Cambridge University has reported the flaw to all the relevant agencies and organisations, and with the publication of their findings it should be expected that many more criminals will now be trying the technique.
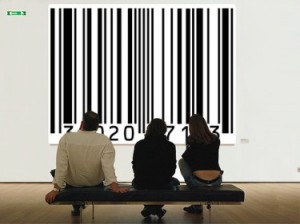
Although this is interesting news in itself, what is more interesting is that it highlights the inherent dangers that we might face because of our implicit trust in technology. It also reminds me directly of the many flaws in RFID technology that were highlighted when it saw more widespread use in retail about five or so years ago. Technology such as Chip-and-PIN and RFID are becoming so ubiquitous that we no longer even consider the ramifications of their use.
When we include things such as mobile phones and social networks, it becomes possible (and increasingly likely) that people could procure incredibly detailed knowledge about our day-to-day lives for nefarious purposes. Your address and date of birth, email addresses and emails, contact lists, diary and calendar, what time you wake up, all the phone calls you make, the websites you visit and articles you read, the music you listen to, the events you will be attending, the photos you take – all of these things, and a lot more, are available simply from a stolen iPhone or other such mobile device. Consider the implications of that for a moment.
Many of us refuse to even acknowledge just how much information we are presenting to the world at an increasing rate. Now, don’t get me wrong, this can also have some amazing advantages to it – and the incredible growth of social networks such as Facebook and Twitter should mean that most of you reading this understand those advantages – but if we’re not careful it can also come at a very expensive price.
Identity and financial theft or, if you are more cynical, government trampling of your civil rights becomes incredibly easy now that so much of our identity and daily activities are becoming digital. The next push in online culture and technology is for the better representation and collation of digital identity, for you as an individual to be represented accurately and interface with websites in such a a manner.
So, what seems like a straight-forward thing for banks to fix in Chip-and-PIN should actually remind us of just how vulnerable we become – especially if we do not seek to understand the technology that we use on a daily (and for many, hourly) basis. Don’t be one of those people who get left behind when it comes to your personal safety and security of information.
Privacy and protection of identity will be one of the fundamental battles society will have to face in the coming digital age, and it is important to make sure that you stay informed about just where and how those battles will take place so that you have the greatest chance of emerging from them unscathed.
[ad name=”Google Adsense-Link Banner x4″]